 Soon Alpha Mainnet
Soon Alpha Mainnet
Badges
About
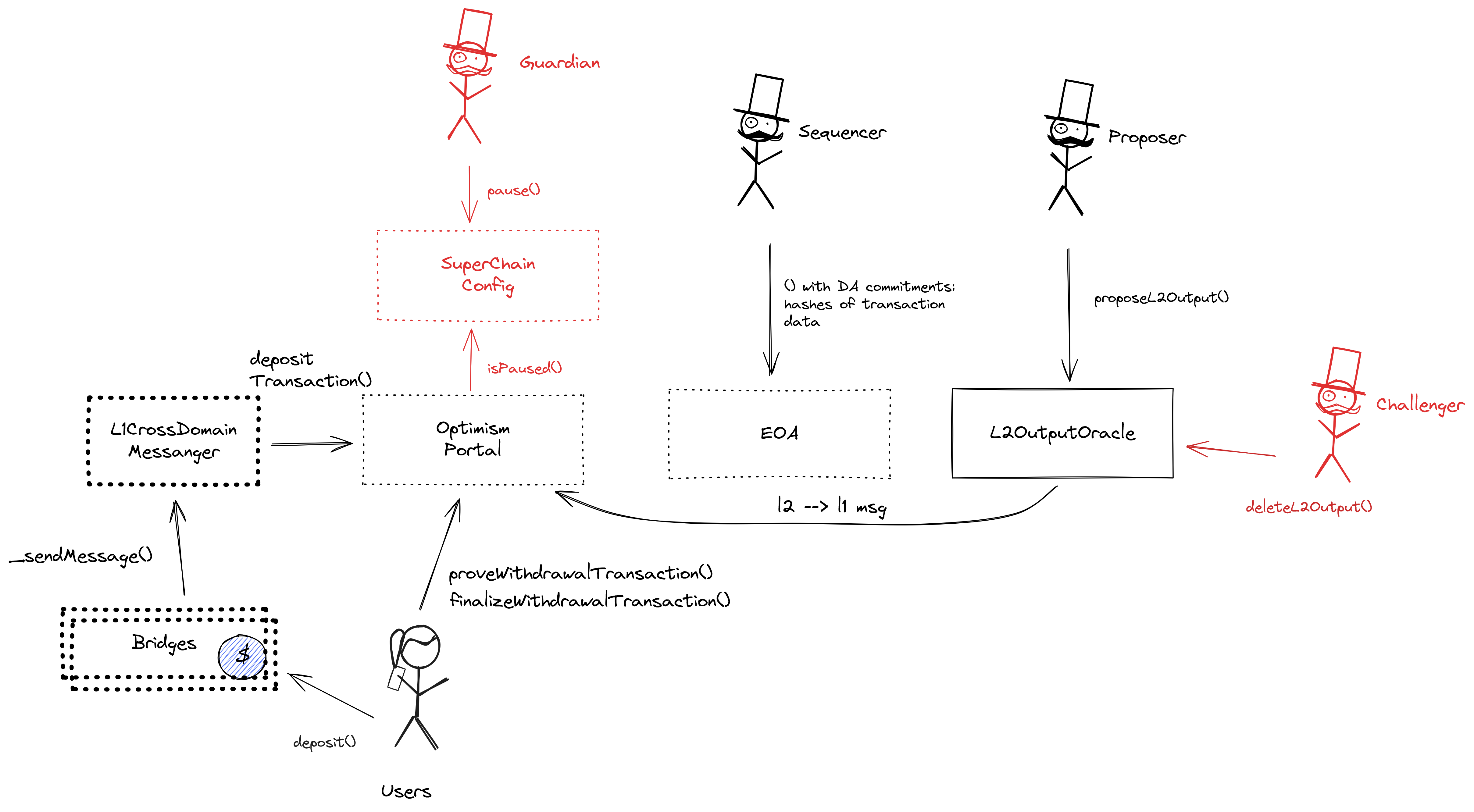
SOON is a Layer 2 chain built on top of the SOON Stack, which itself is based on the OP Stack, but introduces the Decoupled Solana Virtual Machine (SVM).
Badges
About
SOON is a Layer 2 chain built on top of the SOON Stack, which itself is based on the OP Stack, but introduces the Decoupled Solana Virtual Machine (SVM).
Recategorisation
The project will be classified as "Other" due to its specific risks that set it apart from the standard classifications.
The project will move to Others because:
Consequence: projects without a proper proof system fully rely on single entities to safely update the state. A malicious proposer can finalize an invalid state, which can cause loss of funds.
Learn more about the recategorisation here.
Funds can be stolen if
Funds can be lost if
Funds can be frozen if
MEV can be extracted if
Sequencer failure
Self sequenceState validation
NoneCurrently the system permits invalid state roots. More details in project overview.
Data availability
ExternalExit window
NoneThere is no window for users to exit in case of an unwanted regular upgrade since contracts are instantly upgradable.
Proposer failure
Cannot withdrawOnly the whitelisted proposers can publish state roots on L1, so in the event of failure the withdrawals are frozen.
Fraud proofs are not enabled
OP Stack projects can use the OP fault proof system, already being deployed on some. This project though is not using fault proofs yet and is relying on the honesty of the permissioned Proposer and Challengers to ensure state correctness. The smart contract system permits invalid state roots.
Funds can be stolen if an invalid state root is submitted to the system (CRITICAL).
Data is posted to EigenDA
Transactions roots are posted onchain and the full data is posted on EigenDA. Since the ServiceManager bridge is not used, availability of the data is not verified against EigenDA operators, meaning that the Sequencer can single-handedly publish unavailable commitments.
Funds can be lost if the sequencer posts an unavailable transaction root (CRITICAL).
Funds can be lost if the data is not available on the external provider (CRITICAL).
- EigenDA Docs - Overview
- Derivation: Batch submission - OP Mainnet specs
- BatchInbox - Etherscan address
- OptimismPortal.sol - Etherscan source code, depositTransaction function
The system has a centralized operator
The operator is the only entity that can propose blocks. A live and trustworthy operator is vital to the health of the system.
MEV can be extracted if the operator exploits their centralized position and frontruns user transactions.
Users can force any transaction
Because the state of the system is based on transactions submitted on the underlying host chain and anyone can submit their transactions there it allows the users to circumvent censorship by interacting with the smart contract on the host chain directly.
Regular exit
The user initiates the withdrawal by submitting a regular transaction on this chain. When the block containing that transaction is finalized the funds become available for withdrawal on L1. The process of block finalization takes a challenge period of 7d to complete. Finally the user submits an L1 transaction to claim the funds. This transaction requires a merkle proof.
Funds can be frozen if the centralized validator goes down. Users cannot produce blocks themselves and exiting the system requires new block production (CRITICAL).
Forced exit
If the user experiences censorship from the operator with regular exit they can submit their withdrawal requests directly on L1. The system is then obliged to service this request or halt all withdrawals, including forced withdrawals from L1 and regular withdrawals initiated on L2. Once the force operation is submitted and if the request is serviced, the operation follows the flow of a regular exit.
Solana Virtual Machine is supported
OP stack chains are usually pursuing the EVM Equivalence model. But Soon implements the rust-based Solana virtual machine (SVM) which uses parallel processing.
The system uses the following set of permissioned addresses:
Challenger is an actor allowed to challenge or delete state roots proposed by a Proposer.
Guardian is an actor allowed to pause deposits and withdrawals.
Proposer is an actor allowed to post new state roots of the current layer to the host chain.
- A Gnosis Safe with 2 / 4 threshold.
- Can act on behalf of ProxyAdmin.
- Can change the configuration of AddressManager (acting via ProxyAdmin) - set and change address mappings.
- Can upgrade the implementation of L2OutputOracle, SystemConfig, OptimismPortal, L1ERC721Bridge, SuperchainConfig (acting via ProxyAdmin).
- Can upgrade the implementation of L1StandardBridge (acting via ProxyAdmin) - upgrading the bridge implementation can give access to all funds escrowed therein.
A Sequencer.
A Guardian.
A Challenger.
A Proposer.
The system consists of the following smart contracts on the host chain (Ethereum):
Contains a list of proposed state roots which Proposers assert to be a result of block execution. Currently only the PROPOSER address can submit new state roots.
Upgrade delay: No delay
The main entry point to deposit funds from host chain to this chain. It also allows to prove and finalize withdrawals. This version (originally from SOON) of the OptimismPortal is modified to support Solana addresses. It also disallows ERC20 token deposits. Has a MIN_BRIDGE_VALUE set to 0.001 ETH. This contract stores the following tokens: ETH.
Upgrade delay: No delay
Upgrade delay: No delay
- Can be used to configure AddressManager - set and change address mappings.
- Can be used to upgrade implementation of L2OutputOracle, SystemConfig, OptimismPortal, L1ERC721Bridge, SuperchainConfig.
- Can be used to upgrade implementation of L1StandardBridge - upgrading the bridge implementation can give access to all funds escrowed therein.
Legacy contract used to manage a mapping of string names to addresses. Modern OP stack uses a different standard proxy system instead, but this contract is still necessary for backwards compatibility with several older contracts.
Sends messages from host chain to this chain, and relays messages back onto host chain. In the event that a message sent from host chain to this chain is rejected for exceeding this chain’s epoch gas limit, it can be resubmitted via this contract’s replay function.
This is NOT the shared SuperchainConfig contract of the OP stack Superchain but rather a local fork. It manages the PAUSED_SLOT, a boolean value indicating whether the local chain is paused, and GUARDIAN_SLOT, the address of the guardian which can pause and unpause the system.
Upgrade delay: No delay
The main entry point to deposit ETH from host chain to this chain. This version (originally from SOON) is modified to support Solana addresses. It requires specifying the destination SOL address and removes support for ERC20 tokens. This contract can store any token.
Upgrade delay: No delay
Value Secured is calculated based on these smart contracts and tokens:
Main entry point for users depositing ERC20 token that do not require custom gateway.
Upgrade delay: No delay
Main entry point for users depositing ETH.
Upgrade delay: No delay
The current deployment carries some associated risks:
Funds can be stolen if a contract receives a malicious code upgrade. There is no delay on code upgrades (CRITICAL).


